Protecting Your Social Accounts With Two-Step Authentication That Verifying by Sending SMS Message

The continuous security threats that we are exposed in our use of online services has made the traditional user / password binomial to authenticate ourselves in them is not enough. Two-step authentication came in to secure those transactions, but this mechanism is not infallible.
In fact the most popular system to complete that identity verification process is sending an SMS message , but as experts explain, this system is not without security problems. Fortunately there are other alternatives: we discover the most outstanding.
SMS is (much) better than nothing
Although as we will see next two-step verification systems that rely on SMS messages are not the panacea , they are much better than not activate that verification in two steps .
The reason is simple: when you do not use one of these systems, if someone wants to steal your data “only” you will need to collect your username and password. With two-step authentication based on SMS, you will need your user, your password and access your text messages to be able to supplant your identity.
This is what cyber attacks do with techniques like the so-called ‘SIM swap’ in which someone gets the data they need to pretend to be you and, with some social engineering, get your mobile operator to redirect your number Mobile to another . This type of techniques have long been used in countries such as the United Kingdom , where a cyber-attacker obtained bank details of his victim through phishing techniques and then use them to redirect his number to another under his control. From there, access to their accounts was feasible.
Nor does it help to know that SMS messages can be intercepted thanks to the fact that among other things the SS7 connection system on which mobile communications are based is vulnerable to certain attacks, and thanks to that it is possible to capture those messages and that the cyber-attacker Our identity to gain access to those protected services with two-step verification via SMS.
Google Authenticator, a great choice
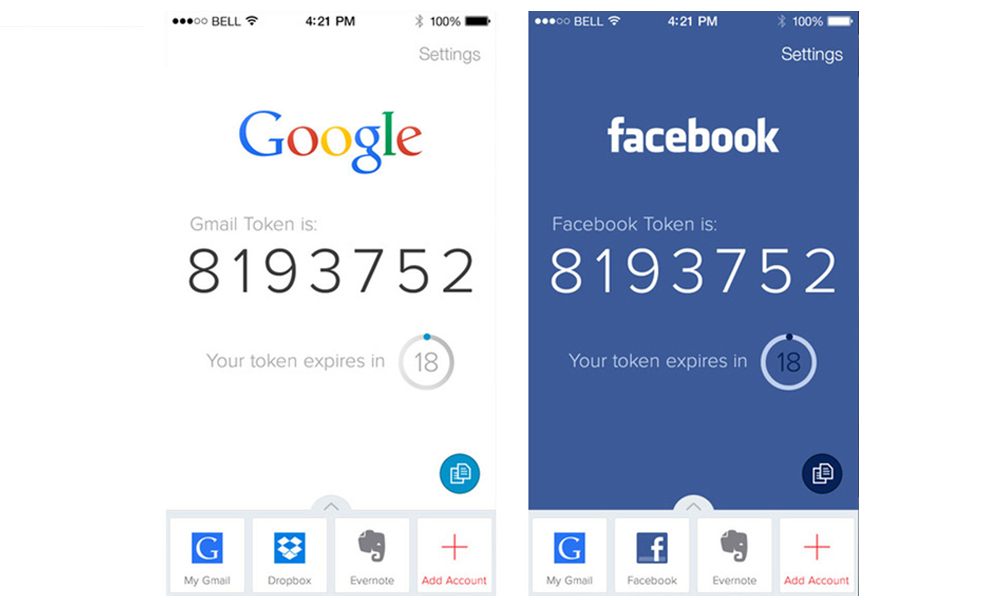
In order to avoid such threats the ideal thing is to prevent someone from “cheating” our telephone company, and that is where services such as Google Authenticator ( Google Play, App Store ) come in, whose mobile application is an excellent alternative for this type of scenarios.

There are other very similar ones like Authy ( Google Play, App Store) that even offer even more options (it is compatible with Google Authenticator, for example), and in both cases the idea is the same: the application generates a code in our device every few Seconds, and that “token” is the one that serves to log in to the service that we have configured with this two-step verification system.
Not all services that allow 2-step verification are compatible with these systems and relegate us to SMS, but increasingly offer this system that significantly improves the security of our accounts.
Our recommendation, of course, is that you always use this method even if it is limited to SMS messages . Keeping in mind that massive password thefts are the order of the day, that extra layer of security will make you breathe (a little) quieter in the face of such threats.
Google Authenticator Video














